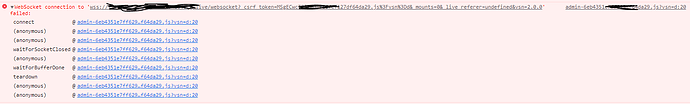
I had to use traefik as my default proxy. Most of the configuration is fine. But my Firezone setup i run in to the a red icon websocket error. I found this FAQ Troubleshoot | Firezone I have no idea what has to be set in my traefik config?
Has anyone an idea how to solve this issue?
x-deploy: &default-deploy
restart_policy:
condition: unless-stopped
delay: 5s
window: 120s
update_config:
order: start-first
version: "3.7"
services:
traefik:
container_name: traefik
image: "traefik:latest"
command:
- --entrypoints.web.address=:80
- --entrypoints.websecure.address=:443
- --providers.docker
- --log.level=ERROR
- --certificatesresolvers.leresolver.acme.httpchallenge=true
- --certificatesresolvers.leresolver.acme.email=EMAIL
- --certificatesresolvers.leresolver.acme.storage=./acme.json
- --certificatesresolvers.leresolver.acme.httpchallenge.entrypoint=web
- --api.dashboard=true
ports:
- "80:80"
- "443:443"
volumes:
- "/var/run/docker.sock:/var/run/docker.sock:ro"
- "./acme.json:/acme.json"
labels:
- "traefik.http.routers.http-catchall.rule=hostregexp(`{host:.+}`)"
- "traefik.http.routers.http-catchall.entrypoints=web"
- "traefik.http.routers.http-catchall.middlewares=redirect-to-https"
- "traefik.http.middlewares.redirect-to-https.redirectscheme.scheme=https"
- "traefik.enable=true"
- "traefik.http.routers.api.entrypoints=websecure"
- "traefik.http.routers.dashboard.rule=Host(`traefik.domain.xx`)&& (PathPrefix(`/api`) || PathPrefix(`/dashboard`))"
- "traefik.http.routers.dashboard.service=api@internal"
- "traefik.http.routers.dashboard.middlewares=auth"
- "traefik.http.middlewares.auth.basicauth.users=username:HASH"
- traefik.docker.network=firezone_firezone-network
networks:
firezone-network:
ipv4_address: 172.25.0.10
firezone:
image: firezone/firezone
ports:
- 51820:51820/udp
env_file:
# This should contain a list of env vars for configuring Firezone.
# See https://docs.firezone.dev/reference/env-vars for more info.
- ${FZ_INSTALL_DIR:-.}/.env
volumes:
# IMPORTANT: Persists WireGuard private key and other data. If
# /var/firezone/private_key exists when Firezone starts, it is
# used as the WireGuard private. Otherwise, one is generated.
- ${FZ_INSTALL_DIR:-.}/firezone:/var/firezone
labels:
# Basic access configuration
- traefik.enable=true
- traefik.docker.network=portainer_default
# Redirect http to https
- traefik.http.routers.firezone_http.entrypoints=web
- traefik.http.routers.firezone_http.rule=Host(`firezone.domain.xx`)
- traefik.http.middlewares.firezone_redirect.redirectscheme.scheme=https
- traefik.http.routers.firezone_http.middlewares=firezone_redirect
# Https
- traefik.http.routers.firezone_https.entrypoints=websecure
- traefik.http.routers.firezone_https.rule=Host(`firezone.domain.xx`)
- traefik.http.routers.firezone_https.tls=true
- traefik.http.routers.firezone_https.tls.certresolver=leresolver
- traefik.http.services.firezone.loadbalancer.server.port=13000
- traefik.http.routers.frontend.service=vpn
cap_add:
# Needed for WireGuard and firewall support.
- NET_ADMIN
- SYS_MODULE
sysctls:
# Needed for masquerading and NAT.
- net.ipv6.conf.all.disable_ipv6=0
- net.ipv4.ip_forward=1
- net.ipv6.conf.all.forwarding=1
depends_on:
- postgres
networks:
firezone-network:
ipv4_address: 172.25.0.100
ipv6_address: 2001:3990:3990::99
deploy:
<<: *default-deploy
postgres:
image: postgres:15
volumes:
- postgres-data:/var/lib/postgresql/data
environment:
POSTGRES_DB: ${DATABASE_NAME:-firezone}
POSTGRES_USER: ${DATABASE_USER:-postgres}
POSTGRES_PASSWORD: ${DATABASE_PASSWORD:?err}
networks:
- firezone-network
deploy:
<<: *default-deploy
update_config:
order: stop-first
volumes:
portainer_data:
postgres-data:
networks:
firezone-network:
enable_ipv6: true
driver: bridge
ipam:
config:
- subnet: 172.25.0.0/16
- subnet: 2001:3990:3990::/64
gateway: 2001:3990:3990::1```