I’ve used this feature with another provider. Routing all egress traffic via a particular peer. Instead of routing traffic via the Firezone host server, it would be sent to a particular peer that authorized such traffic which then masquerades the outbound traffic.
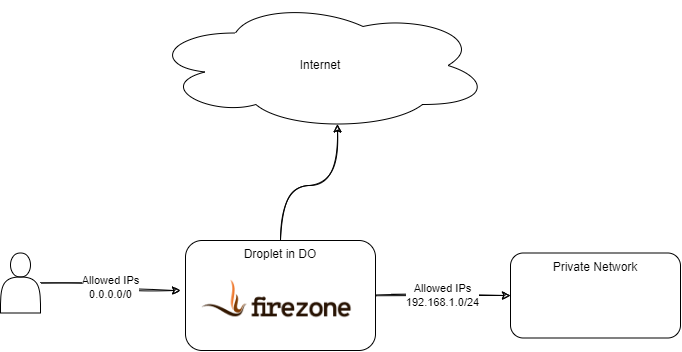
The use case is similar to Using Firezone as a NAT Gateway, but setup to send traffic to a specific peer for egress. The potential use case would be if you have a corporate network and you need to access an IP restricted resource from that network, but your Firezone server is located in a cloud provider.